Best – Brutus Password Cracker Download For Windows / Android Devices
Brutus Password 2024 Cracker is a password cracking designed for security professionals to test the strength of passwords in different authentication protocols.
Brutus Password Cracker – Security experts may assess the reliability of passwords for systems and apps using Brutus, a remote internet password cracking tool. It is often used in network security evaluations and penetration testing. HTTP, POP3, FTP, Telnet, and many more authentication protocols are supported by Brutus. It’s crucial to keep in mind that although Brutus may be a helpful tool for security testing, it can also be used for improper or immoral activities like hacking or unauthorized system access. It’s crucial to utilise these technologies sensibly, within the boundaries of the law, and in accordance with moral standards.
It’s crucial to keep in mind that although Brutus Password Cracker For Android may be a helpful tool for security testing, it can also be used for improper or immoral activities like hacking or unauthorised system access. It’s crucial to utilize these technologies sensibly, within the boundaries of the law, and in accordance with moral standards.
Is Brutus forbidden?
A: Brutus Password Cracker For Mac is a tool with both legitimate and illegitimate uses. It is not unlawful if carried out with consent and for morally and legally acceptable reasons, such as security testing. However, it is unlawful if used for immoral or illegal activities, such as hacking or unauthorised system access.
Is Brutus liberated?
Brutus is not a free tool, to be honest. It is a commercial tool, and using calls for a license.
Which authentication protocols can I use with Brutus?
A: Many different authentication protocols are supported by Brutus, including HTTP, POP3, FTP, Telnet, and many more.
How does Brutus function?
A: In order to break passwords, Brutus either use a dictionary attack or a brute-force assault. Until the right password is discovered, it checks a list of words from a dictionary file or tries every possible character combination.
Is it OK to use Brutus to test security?
A: As long as the owner of the system or application being tested has given permission, using Brutus for security testing is allowed.
Can any password be cracked using Brutus?
A: No, Brutus Password Cracker Download is unable to decipher every password. Strong and complicated passwords that include a mix of capital and lowercase characters, digits, and symbols may be difficult to break using brute-force or dictionary attacks.
Features Of Brutus Password Cracker
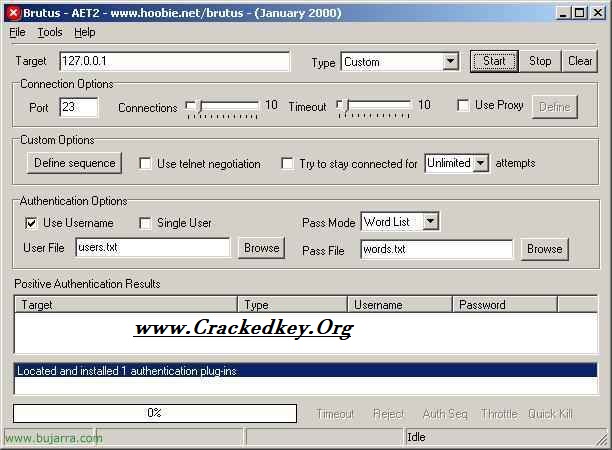
- Protocols for authentication: Brutus is compatible with a wide range of authentication standards, including HTTP, POP3, FTP, Telnet, and many more.
- This enables security experts to evaluate the security of passwords used with various systems and apps.
- Dictionary attack: To break passwords, Brutus use a dictionary attack.
- It looks to see if any of the words in a list from a dictionary file match the password being tried.
- Brutus also supports brute-force assaults, which include attempting every conceivable character combination up until the right password is discovered.
- Multi-threaded: Brutus is a multi-threaded programme, allowing it to break passwords on many targets at once.
- Parameters that may be changed: Brutus gives users the option to change a variety of parameters, including the character set used for brute-force attacks.
- the dictionary file used for dictionary attacks, and the number of threads used for multi-threading.
Main Characteristics Of Brutus Password Breaker Or Cracker
- Ease of Use: Brutus Password software boasts an intuitive user interface, making it accessible even to those with limited technical expertise. Users can navigate through its functionalities effortlessly, saving time and minimizing frustration.
- Versatility: This software caters to a wide range of security needs, allowing users to generate, store, and manage passwords with ease. Whether for personal use or within an organizational setting, Brutus Password software adapts to various contexts seamlessly.
- Robust Security Features: Security is paramount, and Brutus Password software doesn’t compromise in this aspect. It employs advanced encryption algorithms to safeguard sensitive information effectively. Users can trust that their passwords remain secure from unauthorized access.
- Customization Options: One size doesn’t fit all, and Brutus Password software recognizes this. It offers customization options, allowing users to tailor settings according to their preferences and specific security requirements.
- Reliability and Stability: Users praise Brutus Password software for its reliability and stability. It operates smoothly without glitches or crashes, providing a consistent user experience.
- Regular Updates: The developers behind Brutus Password software are committed to improving its functionality and addressing any potential vulnerabilities. Regular updates ensure that users benefit from the latest security enhancements and features.
- Excellent Support: In case of any queries or issues, users can rely on prompt and helpful customer support provided by the Brutus Password software team. Their responsiveness and dedication contribute to a positive user experience.
- Cost-Effectiveness: Brutus Password software offers excellent value for money. Its feature-rich capabilities come at a reasonable price point, making it an attractive option for individuals and businesses alike.
Related Program’s For Download & Use
Proteus Crack
Boom 3D Crack
Windows Activator
Listary Pro Crack
How To Install Brutus Password Cracker For Android & Windows?
- Go to the vendor’s website and download the Brutus Password 2023 Cracker installer.
- To begin installing the downloaded file, double-click it.
- To choose an installation location and accept the licence agreement, just follow the installation wizard’s instructions.
- Launch the Brutus programme after the installation is complete.
- the authentication protocol, IP address, port number, and login information—all of which are required for the target system or application.
- Select the attack strategy, such as brute-force or dictionary, and alter the settings as necessary.
- Attack first, then wait for Brutus to figure out the password.