.NET Reactor 6.9.0.0 Crack Activated Setup Download (FREE)
.NET Reactor Crack extremely awesome program which allows for easy management of all types of Applications, Software, License Agreements, Codes Protection, Modern Licensing systems, All Operating Systems Languages Supported. Fully upgraded software which allows to easily management all the types of Data Encryption & License Agreements.
.Net Reflector Download! (2023) – New version
A user can easily Implement New Objects with .Net Reactor Download, Work On Visual OS Languages, Write New Scripts, Codes Protection, Traditional Institutions, Robot Languages, Agreements, Supported Android, iOS, Microsoft & Mac OS Programs. Still used in the hands of IT Professionals, Experts, etc.
.NET Reactor Command Line also has a function called “Control Flow Obfuscation,” which converts the application code into a difficult to read and comprehend format. This makes it more difficult for attackers to decipher the application’s structure and logic.
What Is It?
Eziriz .NET Reactor Crack is a software program that encrypts and obfuscates the code of.NET applications. Software developers typically utilize it to safeguard their intellectual property and avoid reverse engineering of their programs.
How to use .NET Reactor?
Install & Setup:
- Download and install complete setup.
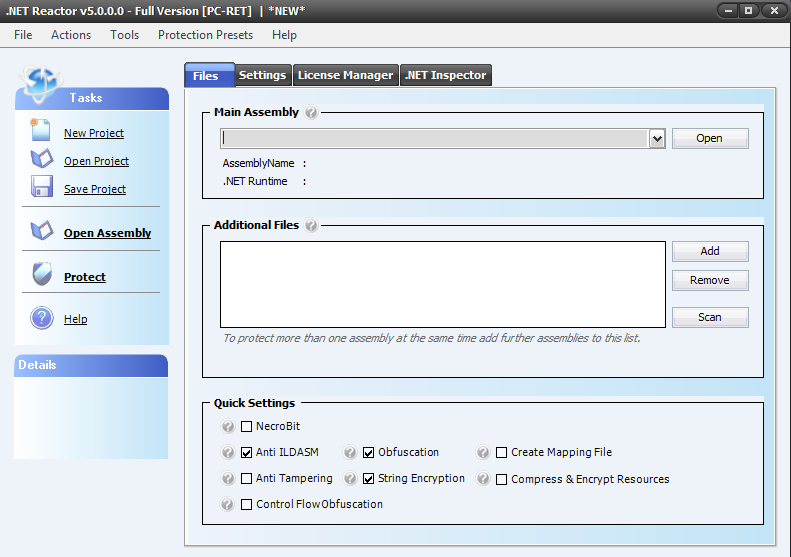
- Launch the app and learn its UI.
Project Creation:
- Enter your .NET application’s executable or DLL and protection choices to create a new project in .NET Reactor.
Safety Settings:
- It enables customizable protection options.
- Obfuscation, renaming, and optimization to prevent reverse engineering.
- String Encryption with Protecting string literals.
- Obfuscating control flow by changing instruction sequence.
- Protecting embedded resources.
- Checking for assembly tampering.
- Controlling application usage via license checks.
License and Activation:
- Trial durations, feature limits, and licensing conditions are configurable.
Build and Defense:
- Using this software, construct your protected assembly.
- The gadget will safeguard your assembly.
Testing and deployment:
- To confirm your application’s operation, test the protected assembly.
- If you’re utilizing licensing, deploy the protected assembly to your clients with the license files.
Upkeep & Updates:
- Keep up with upgrades for the latest features and security.
.NET Reactor Torrent Newest Features:
- Mostly used in the hands of Experts, Developers, Compression Supports.
- Modernized Licensing System, Executable Files, Assembling & Dessambling.
- All the Net-Frameworks Supported, HTML, Python & Cobra Coding.
- A fully Modernized Assembly Stimulation, Supported SilverLight, WPF & others.
- Totally Clean Objects, Additional Protection Layers & many others.
Minimum System Requirements
- Microsoft Windows & Linux.
- 2.0 or Faster Processor.
- 1GB OS RAM.
- 100MB Free HDD Space.
.NET Reactor Master Key:
M21N-C32X-G1D5-6F7U-8PI7-UO89-YIUT-YR7T-ERW6-R4HJ-5GCN
6JGF-5848-97OP-U98O-7YIU-TYR4-YRT5-KH4J-GHFX-21CV-M2SE
.NET Reactor Keygen:
8G78-7UO8-OIUY-T3W4-RTE3-JFG3-2F1B-23VC-N1CF-CG7Y-8U7R
C32V-1FC5-6T7Y-IG89-YFO7-U98P-7O9I-Y8TF-U4J5-31G8-Y798-Y456
.NET Reactor License Key:
78UO-Y6FK-4Y5J-GF43-NX21-2313-C2N1-VV23-3F54-CJX8-7IYY-86CG
21NF-X4KG-CY78-9YF7-O76X-FR4U-3XF1-JGCF-4Y98-ER76-F4J2-3GC1
Related Developing Scripting Tools
InstallShield Crack
Astah Professional Crack
Bootstrap Studio Crack
How To Use & Install .NET Reactor Torrent?
- Professionally used in the hands of Developers, Programmers & Apps Protection.
- Get the latest version of .NET Reactor Free Download.
- Un-Extract downloaded set up in the OS & Install.
- After Installation, Double-Tap on the installed software icon.
- After Running, Let’s Use All The Objects Who Allows You To Protect Files From The Online Threats.